#include <config.h>
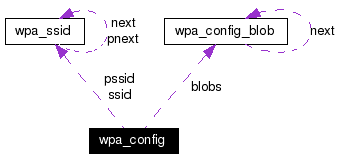
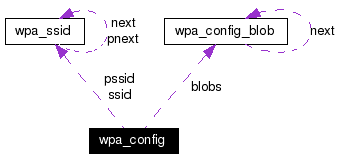
Collaboration diagram for wpa_config:
Data Fields | |
| wpa_ssid * | ssid |
| Head of the global network list. | |
| wpa_ssid ** | pssid |
| Per-priority network lists (in priority order). | |
| int | num_prio |
| Number of different priorities used in the pssid lists. | |
| int | eapol_version |
| IEEE 802.1X/EAPOL version number. | |
| int | ap_scan |
| AP scanning/selection. | |
| char * | ctrl_interface |
| Parameters for the control interface. | |
| char * | ctrl_interface_group |
| Control interface group (DEPRECATED). | |
| int | fast_reauth |
| EAP fast re-authentication (session resumption). | |
| char * | opensc_engine_path |
| Path to the OpenSSL engine for opensc. | |
| char * | pkcs11_engine_path |
| Path to the OpenSSL engine for PKCS#11. | |
| char * | pkcs11_module_path |
| Path to the OpenSSL OpenSC/PKCS#11 module. | |
| char * | driver_param |
| Driver interface parameters. | |
| unsigned int | dot11RSNAConfigPMKLifetime |
| Maximum lifetime of a PMK. | |
| unsigned int | dot11RSNAConfigPMKReauthThreshold |
| PMK re-authentication threshold. | |
| unsigned int | dot11RSNAConfigSATimeout |
| Security association timeout. | |
| int | update_config |
| Is wpa_supplicant allowed to update configuration. | |
| wpa_config_blob * | blobs |
| Configuration blobs. | |
This data structure is presents the per-interface (radio) configuration data. In many cases, there is only one struct wpa_config instance, but if more than one network interface is being controlled, one instance is used for each.
Definition at line 69 of file config.h.
|
|
AP scanning/selection. By default, wpa_supplicant requests driver to perform AP scanning and then uses the scan results to select a suitable AP. Another alternative is to allow the driver to take care of AP scanning and selection and use wpa_supplicant just to process EAPOL frames based on IEEE 802.11 association information from the driver. 1: wpa_supplicant initiates scanning and AP selection (default). 0: Driver takes care of scanning, AP selection, and IEEE 802.11 association parameters (e.g., WPA IE generation); this mode can also be used with non-WPA drivers when using IEEE 802.1X mode; do not try to associate with APs (i.e., external program needs to control association). This mode must also be used when using wired Ethernet drivers. 2: like 0, but associate with APs using security policy and SSID (but not BSSID); this can be used, e.g., with ndiswrapper and NDIS drivers to enable operation with hidden SSIDs and optimized roaming; in this mode, the network blocks in the configuration are tried one by one until the driver reports successful association; each network block should have explicit security policy (i.e., only one option in the lists) for key_mgmt, pairwise, group, proto variables. |
|
|
Parameters for the control interface. If this is specified, wpa_supplicant will open a control interface that is available for external programs to manage wpa_supplicant. The meaning of this string depends on which control interface mechanism is used. For all cases, the existance of this parameter in configuration is used to determine whether the control interface is enabled. For UNIX domain sockets (default on Linux and BSD): This is a directory that will be created for UNIX domain sockets for listening to requests from external programs (CLI/GUI, etc.) for status information and configuration. The socket file will be named based on the interface name, so multiple wpa_supplicant processes can be run at the same time if more than one interface is used. /var/run/wpa_supplicant is the recommended directory for sockets and by default, wpa_cli will use it when trying to connect with wpa_supplicant. Access control for the control interface can be configured by setting the directory to allow only members of a group to use sockets. This way, it is possible to run wpa_supplicant as root (since it needs to change network configuration and open raw sockets) and still allow GUI/CLI components to be run as non-root users. However, since the control interface can be used to change the network configuration, this access needs to be protected in many cases. By default, wpa_supplicant is configured to use gid 0 (root). If you want to allow non-root users to use the control interface, add a new group and change this value to match with that group. Add users that should have control interface access to this group. When configuring both the directory and group, use following format: DIR=/var/run/wpa_supplicant GROUP=wheel DIR=/var/run/wpa_supplicant GROUP=0 (group can be either group name or gid) For UDP connections (default on Windows): The value will be ignored. This variable is just used to select that the control interface is to be created. The value can be set to, e.g., udp (ctrl_interface=udp). For Windows Named Pipe: This value can be used to set the security descriptor for controlling access to the control interface. Security descriptor can be set using Security Descriptor String Format (see http://msdn.microsoft.com/library/default.asp?url=/library/en-us/secauthz/security/security_descriptor_string_format.asp). The descriptor string needs to be prefixed with SDDL=. For example, ctrl_interface=SDDL=D: would set an empty DACL (which will reject all connections). |
|
|
Control interface group (DEPRECATED). This variable is only used for backwards compatibility. Group for UNIX domain sockets should now be specified using GROUP=<group> in ctrl_interface variable. |
|
|
Maximum lifetime of a PMK. dot11 MIB variable for the maximum lifetime of a PMK in the PMK cache (unit: seconds). |
|
|
PMK re-authentication threshold. dot11 MIB variable for the percentage of the PMK lifetime that should expire before an IEEE 802.1X reauthentication occurs. |
|
|
Security association timeout. dot11 MIB variable for the maximum time a security association shall take to set up (unit: seconds). |
|
|
Driver interface parameters. This text string is passed to the selected driver interface with the optional struct wpa_driver_ops::set_param() handler. This can be used to configure driver specific options without having to add new driver interface functionality. |
|
|
IEEE 802.1X/EAPOL version number. wpa_supplicant is implemented based on IEEE Std 802.1X-2004 which defines EAPOL version 2. However, there are many APs that do not handle the new version number correctly (they seem to drop the frames completely). In order to make wpa_supplicant interoperate with these APs, the version number is set to 1 by default. This configuration value can be used to set it to the new version (2). |
|
|
EAP fast re-authentication (session resumption). By default, fast re-authentication is enabled for all EAP methods that support it. This variable can be used to disable fast re-authentication (by setting fast_reauth=0). Normally, there is no need to disable fast re-authentication. |
|
|
Number of different priorities used in the pssid lists. This indicates how many per-priority network lists are included in pssid. |
|
|
Path to the OpenSSL engine for opensc. This is an OpenSSL specific configuration option for loading OpenSC engine (engine_opensc.so); if NULL, this engine is not loaded. |
|
|
Path to the OpenSSL engine for PKCS#11. This is an OpenSSL specific configuration option for loading PKCS#11 engine (engine_pkcs11.so); if NULL, this engine is not loaded. |
|
|
Path to the OpenSSL OpenSC/PKCS#11 module. This is an OpenSSL specific configuration option for configuring path to OpenSC/PKCS#11 engine (opensc-pkcs11.so); if NULL, this module is not loaded. |
|
|
Head of the global network list. This is the head for the list of all the configured networks. |
|
|
Is wpa_supplicant allowed to update configuration. This variable control whether wpa_supplicant is allow to re-write its configuration with wpa_config_write(). If this is zero, configuration data is only changed in memory and the external data is not overriden. If this is non-zero, wpa_supplicant will update the configuration data (e.g., a file) whenever configuration is changed. This update may replace the old configuration which can remove comments from it in case of a text file configuration. |
 1.4.2
1.4.2